Security Policies @ Kelvin¶
On this page you will learn about Kelvin's security policy infrastructure achieved to ensure that the security standards are deeply embedded into the organization.
Overview¶
In today's world the progression of the Industry 4.0, commonly referred to as the fourth industrial revolution, this has opened up a plethora of new tools and options for all areas of industry from IT/OT convergence, simpler OT management and deployment, utilizing advanced sub-routines at the edge and tapping powerful computing options without the investment as some examples.
But with this comes a new array of attack vectors that bad actors can utilize to gain unauthorized access into industrial IT and OT systems.
In itself this is not bad news as the programming world has also changed considerably. These can include openly available industrial standards of encryption, audits of open-source and closed-source components, new programming environments that reduces attack vector possibilities and proper awareness of building applications from security perspectives first.
Most important is to ensure that as a company developing software solutions, it must be a top priority to ensure the proper security practices have been embedded into the organization.
Kelvin AI¶
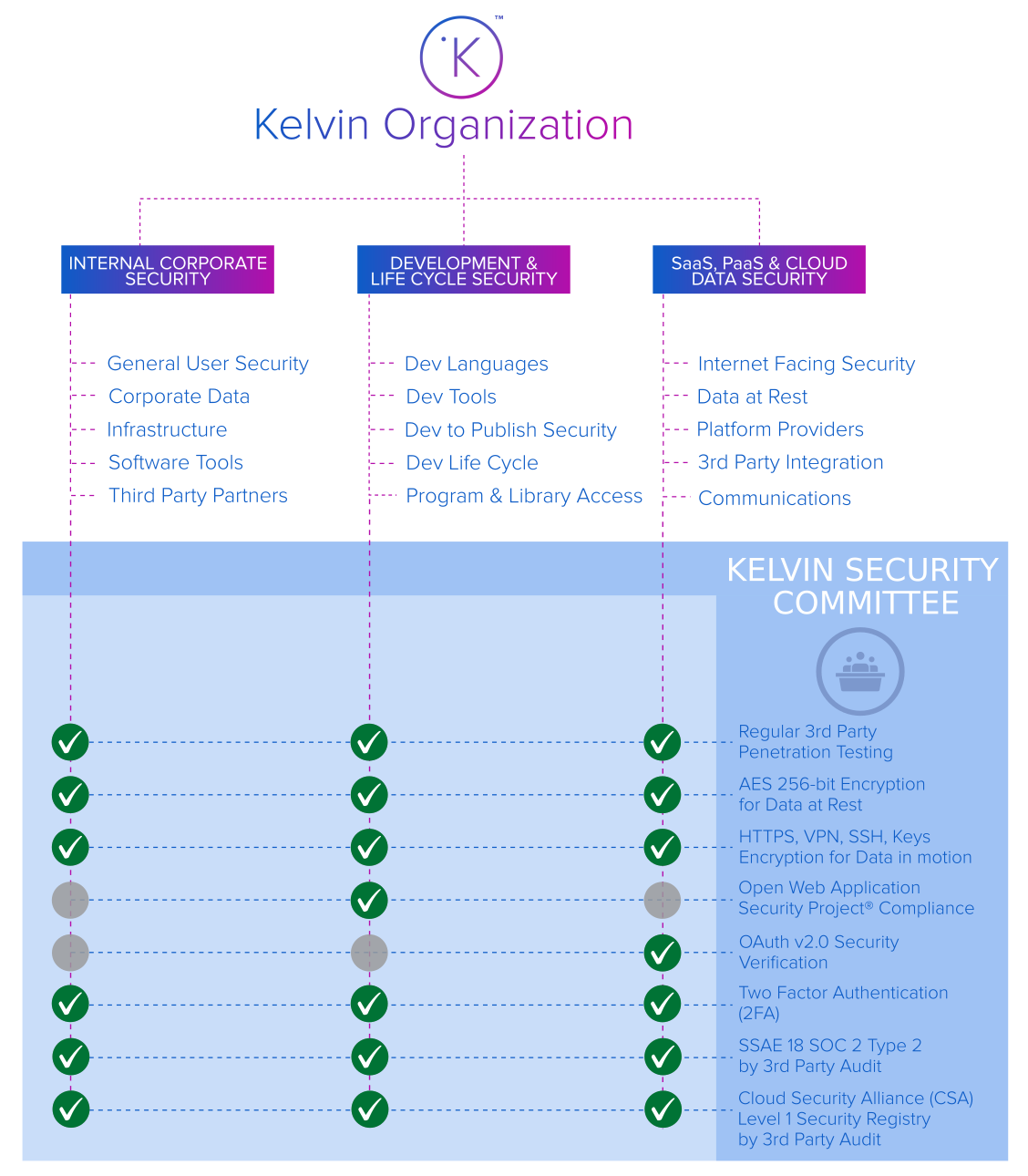
Kelvin has incorporated a strict set of security policies to ensure that the latest security protocols and standards are followed in all critical areas of the organization including;
- Internal corporate access and data security.
- Development tools, programming policies and programming standards security.
- Client's cloud & data security, attack prevention and disaster recovery infrastructure.
Security Team¶
Kelvin has a dedicated security team which handles the daily security aspects for the organization and product delivery. The security team works closely with the IT, development and cloud providers to ensure;
- 24/7 monitoring and alerts on security infrastructure
- Proper security practices are in place for all organizational infrastructure
- All personnel are properly trained on security best practices
- Security monitoring of all development software practices and infrastructure
- Close cooperation with the cloud providers on security related matters
- Compliance of all security related certifications at Kelvin
- Monitor for the latest known security threats and take any preemptive actions to ensure all attack vectors are always minimized.
Security Committee¶
Kelvin has an internal Security Committee that maintains a continuous review of the overall security standards and practices in Kelvin.
- Continually reassess current security protocol in all areas of the organization
- Monitors real-time threat intelligence services for new vulnerabilities or malicious players in the wild
- A network of trusted public and private sources on all security related matters
- Direct links to vendor notifications and security alerts
- Organization of third party security penetration test, security consultancy and security certifications.
Security Practices¶
Data in Motion¶
All communications and endpoints employ the latest encryption standards. The industrial standards depends on the type of communications and will include;
- Using VPN communications between data centers
- Employing the latest HTTPS/TLS encryption standards for all servers such as TLS 1.2, AES_128_GCM, ECDHE_RSA with P-256 and certificates issues by the trusted Sectigo RSA Domain Validation Secure Server CA
- Traceability of actions taken within the communication network
- Using the latest industrial strength encryption for the Kelvin Core communication infrastructure
Data At Rest¶
All data at rest on the any Kelvin servers utilize enterprise grade encryption industrial standards such as AES 256-bit encryption.
Data is logically separated with controls designed to prevent data leakage between independent storage areas.
OWASP Compliance¶
Kelvin Software Development Life Cycle (SDLC) framework is based on industry standards such as the OWASP, which ensures that secure design practices are integrated directly into the design and development process of the Cloud Server.
Risk Management¶
Kelvin maintains a risk management program based on industry guidance.
Risk assessments of various scope are conducted regularly throughout the year, including self and third-party assessments and tests, automated scans, and manual reviews.
Notifications¶
In the unlikely event of a security breach Kelvin has a team in place to take immediate actions to contain, investigate, and mitigate any such breaches.
Any affected customers will be notified in within seventy-two (72) hours of a confirmed unauthorized access to sensitive information (“Security Breach”). Notification will summarize the known details of the Security Breach and the status of Kelvin’s investigation.
Disaster Recovery¶
Kelvin maintains a Disaster Recovery Plan (DRP) for the Cloud Service which includes customer's accounts. The DRP is tested on a regular basis.
To cover data being sent to and stored within the Cloud Service infrastructure, Customer is responsible for ensuring that it implements a service level that corresponds with Customer’s disaster recovery strategy.