Cloud - Edge Communications¶
On this page you will learn about communications between Kelvin's Cloud services and Edge systems.
Overview¶
A fundamental aspect of data exchange is the security and authentication of connections between the Cloud and the Edge. The combination of advanced communication protocols and stringent security measures forms the backbone of a resilient and reliable industrial communication network.
For all communication and authentications systems, Kelvin uses industrial standards that are certified for use in production systems.
For the average client there will be two URL locations in the cloud and unlimited edge systems that will be connected together. Usually these connections are maintained on a continuous 24/7 basis but Kelvin is resilient to edge systems going offline for significant periods of time with no data loss.
There are three main topics to cover in Cloud - Edge communications;
- Main communications links
- Encryption while data is in motion
- Authentication of systems with Internet facing connections
Communications¶
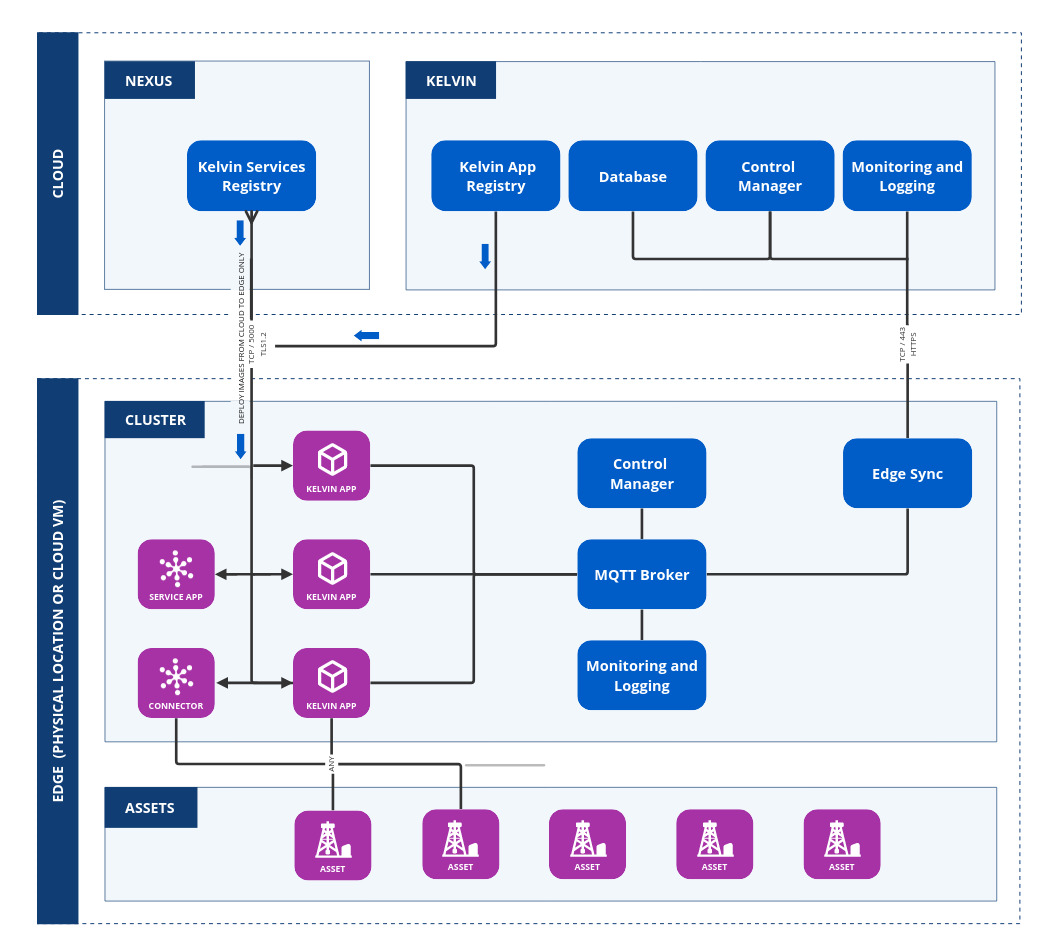
Edge systems in the Cloud-Edge communication architecture always initiate communication. Edge devices do not accept unsolicited incoming communications.
As there can be an unlimited amount of edge devices setup and that it can not be guaranteed that edge devices will be online and able to receive security updates in a timely manner, this security strategy allows for a firewall at each edge system to block all incoming communications. This reduces the vectors of attack available to bad actors even if some internal software has known security flaws.
The cloud environment always acts as the responsive entity and not an initiator. This has the advantage of;
- Security monitoring and telemetry is simplified to only two cloud systems.
- Firewalls can be easily maintained and managed to only accept communications from known edge locations.
- With only two systems to maintain security updates and patching, new security announcements can be tested and implemented fast.
For convenience, some clients may want to install remote access software like ssh or corporate software onto the edge systems. This adds new attack vectors to edge systems for bad actors and should be implemented with care. Kelvin does not monitor or maintain any custom software installed on the edge systems.
Encryption in Motion¶
For image deployment from the image repositories in Kelvin Nexus Repository and Kelvin Cloud servers, Kelvin uses TCP on port 5000 secured with TLS 1.2 encryption. This ensures that data is encrypted during transit to safeguard against potential data breaches or interception. TLS 1.2 provides a reliable level of security, encrypting the data before it leaves the source and decrypting it only when it reaches its intended destination.
All other communication between the edge devices and cloud server use HTTPS over port 443. HTTPS, which incorporates TLS (Transport Layer Security), provides a secure channel over the Internet, encrypting the entire communication session. This ensures that all operational data, commands, and responses between the edge and the cloud are secure from eavesdropping, tampering, or message forgery.
HTTPS is also how users will interact with Kelvin through the Kelvin UI, Kelvin SDK and Kelvin API.
Authentication¶
Each new Edge system registration involves assigning a unique Service Account, which is used as authentication with the cloud servers for all communications. These service accounts are severely limited in scope, possessing only essential permissions needed for their specific functions.
For authentication purposes, all systems adhere to the OAuth2/OIDC protocols. This standard provides a secure and efficient method for managing access, ensuring that each interaction between the Edge systems and cloud servers is authenticated.
Other Communications¶
Apart from the communications between the Edge and Cloud, the other external communications to the Cloud will come from clients through Kelvin UI, Kelvin SDK and Kelvin API. All these services use HTTPS over port 443.
Kelvin does not allow direct communications between the client and Edge systems. All information about the Edge system, like telemetry and data, that clients receive is delivered from the Cloud.
Authentication and access can be initiated with a custom service account or a user account. Permissions available for each authentication will vary depending on the client's corporate policies.
It is important that clients maintain strong security protocols to ensure these authentication credentials do not fall into the hands of bad actors who can use them to gain access to Kelvin.